Published:

As attackers begin using AI to accelerate attacks, personalize deception, and automate multiple stages of intrusion, the traditional Security Operations Center model is no longer fast enough to respond effectively.
Today, organizations are not only facing a higher volume of attacks, but also dealing with threats that are more sophisticated, harder to detect, and faster to execute. In this environment, AI is no longer a “nice-to-have” technology. It is becoming a core capability that enables SOC teams to maintain an effective defense posture.
In the past, executing a targeted cyberattack often required significant time for research, phishing content creation, malware preparation, and system reconnaissance. With AI, many of these steps can now be completed much faster.
AI can help attackers:
What makes this especially concerning is that attackers do not necessarily need entirely new techniques. By using AI to scale operations, increase speed, and lower attack costs, they can already put enormous pressure on enterprise security defenses.
For many years, SOC teams operated effectively through detection rules, alerting systems, and the experience of security analysts. However, as attackers adopt AI, this model is starting to show clear limitations.
The growing volume of logs and alerts makes it increasingly difficult for operations teams to distinguish truly dangerous signals from noise. Without intelligent analysis support, SOC teams can quickly fall into alert fatigue.
If attackers can reduce the time from initial access to data theft to just a few hours, or even a few minutes, SOC teams cannot afford to spend hours validating a single alert. Delayed investigation means losing the critical window to contain the incident.
Modern attacks rarely stay within a single system. They may begin with email, move to user accounts, spread across endpoints and servers, and eventually reach cloud environments and internal data. If the SOC sees only isolated alerts, it becomes difficult to recognize the full attack chain.
AI does not only make SOC faster. It also helps SOC teams make better decisions in an environment flooded with data and alerts.
AI can analyze large volumes of data from endpoints, identities, networks, email systems, and cloud environments to identify abnormal behavior patterns. This is especially useful in attacks that are malware-free, abuse legitimate accounts, or hide within seemingly normal activity.
Instead of requiring analysts to manually open multiple data sources and piece together clues, AI can support them by:
As a result, SOC teams can significantly reduce the time between detection and response.
Not every alert requires immediate escalation. AI can help score risk, group related events, and prioritize incidents with the highest potential business impact. This allows SOC teams to focus resources on what matters most.
AI can support response playbooks such as:
The key is that AI in SOC should act as a force multiplier for human teams, not as a completely uncontrolled decision-maker.
To defend effectively against AI-powered hackers, organizations should not view AI merely as a chatbot or summarization tool. AI needs to be embedded across the broader security operations workflow.
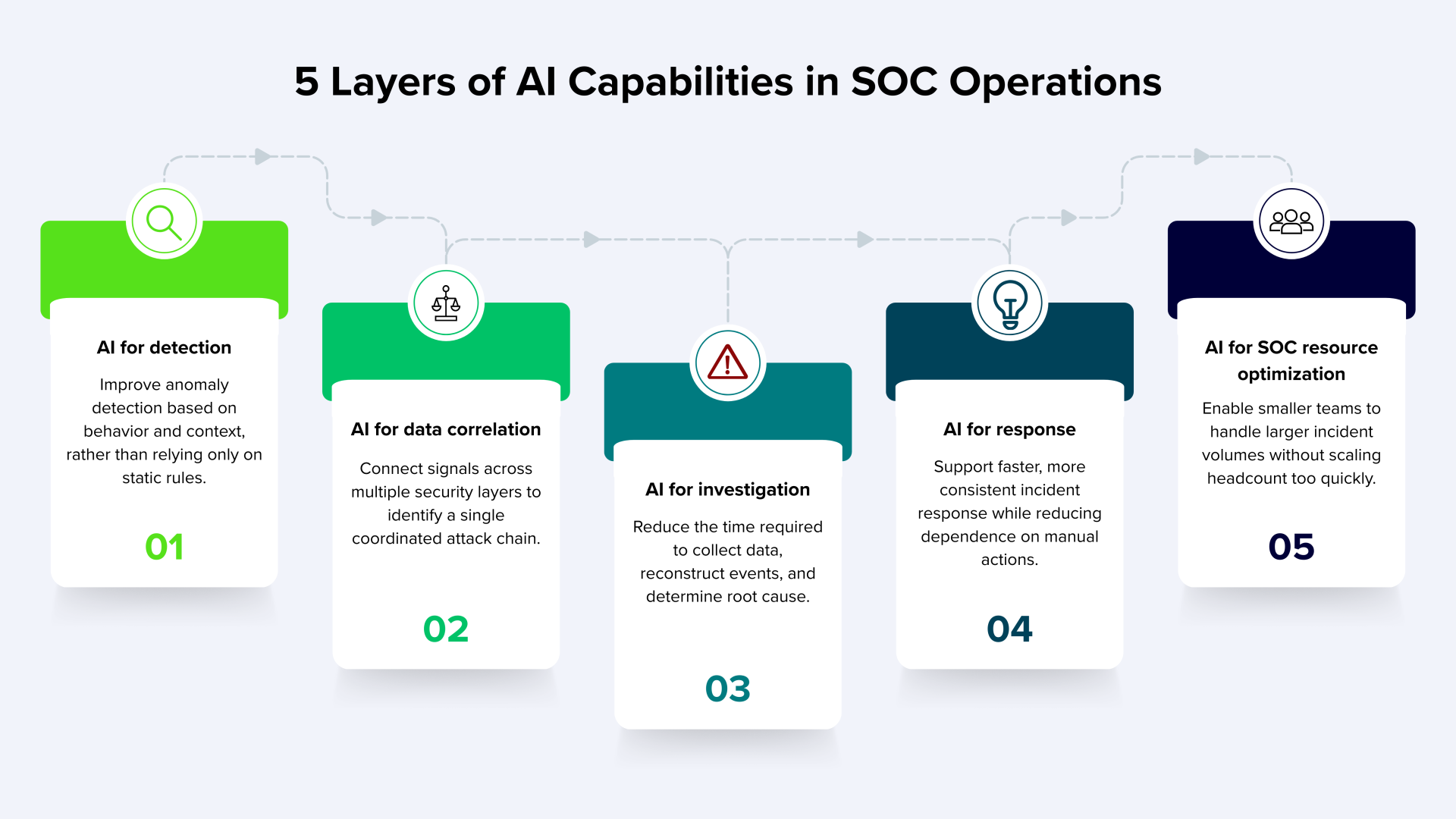
SOC needs AI not because AI is a new trend, but because attackers are already using AI to shorten attack chains, improve deception, automate reconnaissance, and scale intrusions. As attackers become faster, more adaptive, and harder to predict, SOC must evolve from a model of manual monitoring and response into one powered by AI-enhanced detection, investigation, and incident response.
In other words, when attackers use AI to increase offensive power, SOC teams also need AI to maintain defensive strength.
CyberTech provides AI and cybersecurity solutions for enterprises and organizations in Vietnam, with a focus on combining technological capability and operational security requirements in real-world environments.
Contact CyberTech for consultation on the right solution for your organization: